Visibility Built for Control, Not Assumptions
We provide visibility into IT environments based on real assets, connections, and operational context—not incomplete spreadsheets or static documentation.
Our approach focuses on discovering, classifying, and continuously understanding devices across local, network, and hybrid environments.
Asset information is structured to support IT operations, cybersecurity decisions, compliance reporting, and infrastructure planning.
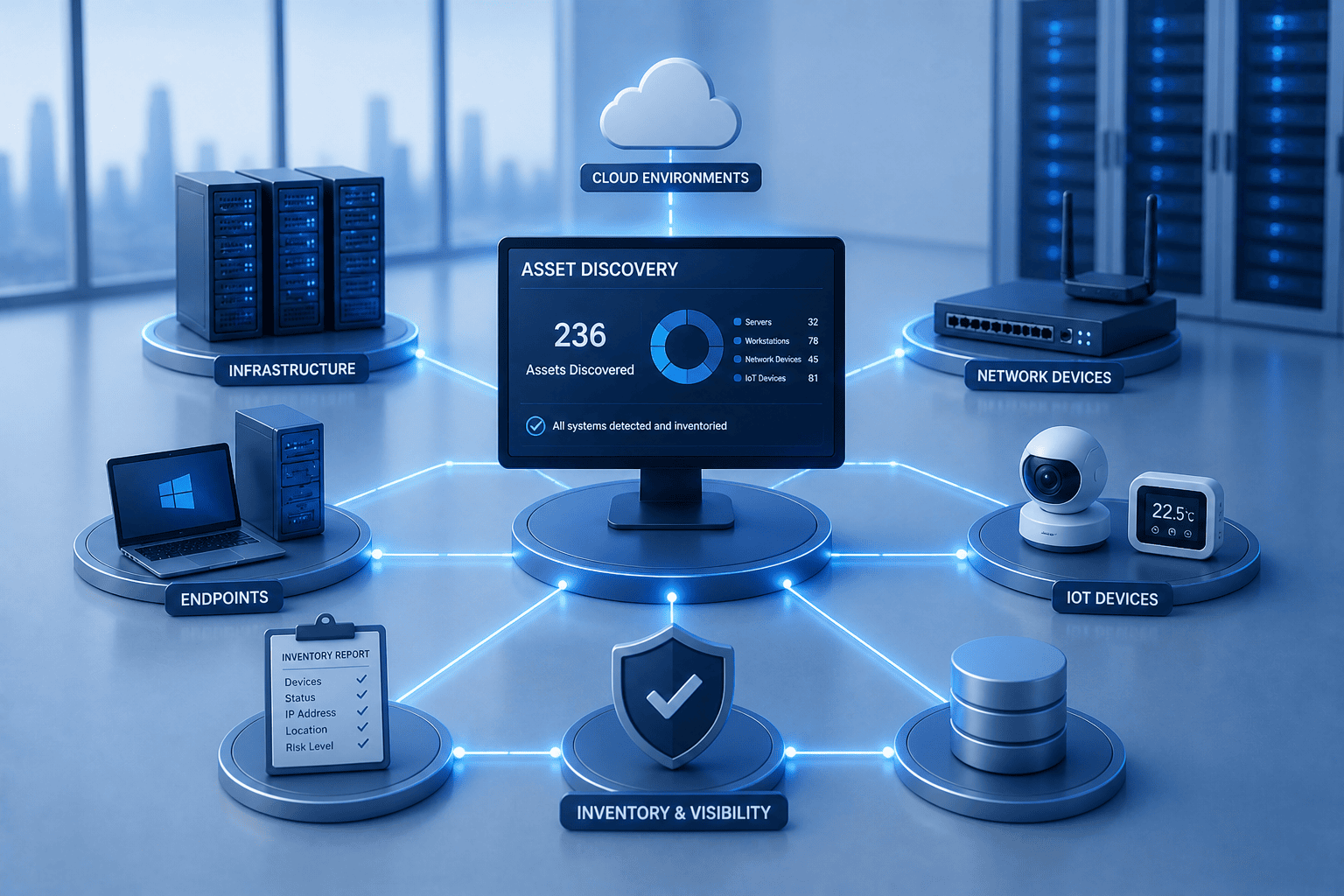
Asset Discovery and Inventory Across IT and IoT
We identify and document devices across local networks, infrastructure environments, endpoints, and connected IoT systems. Discovery helps eliminate blind spots and creates a reliable inventory foundation for operations, security, and planning.
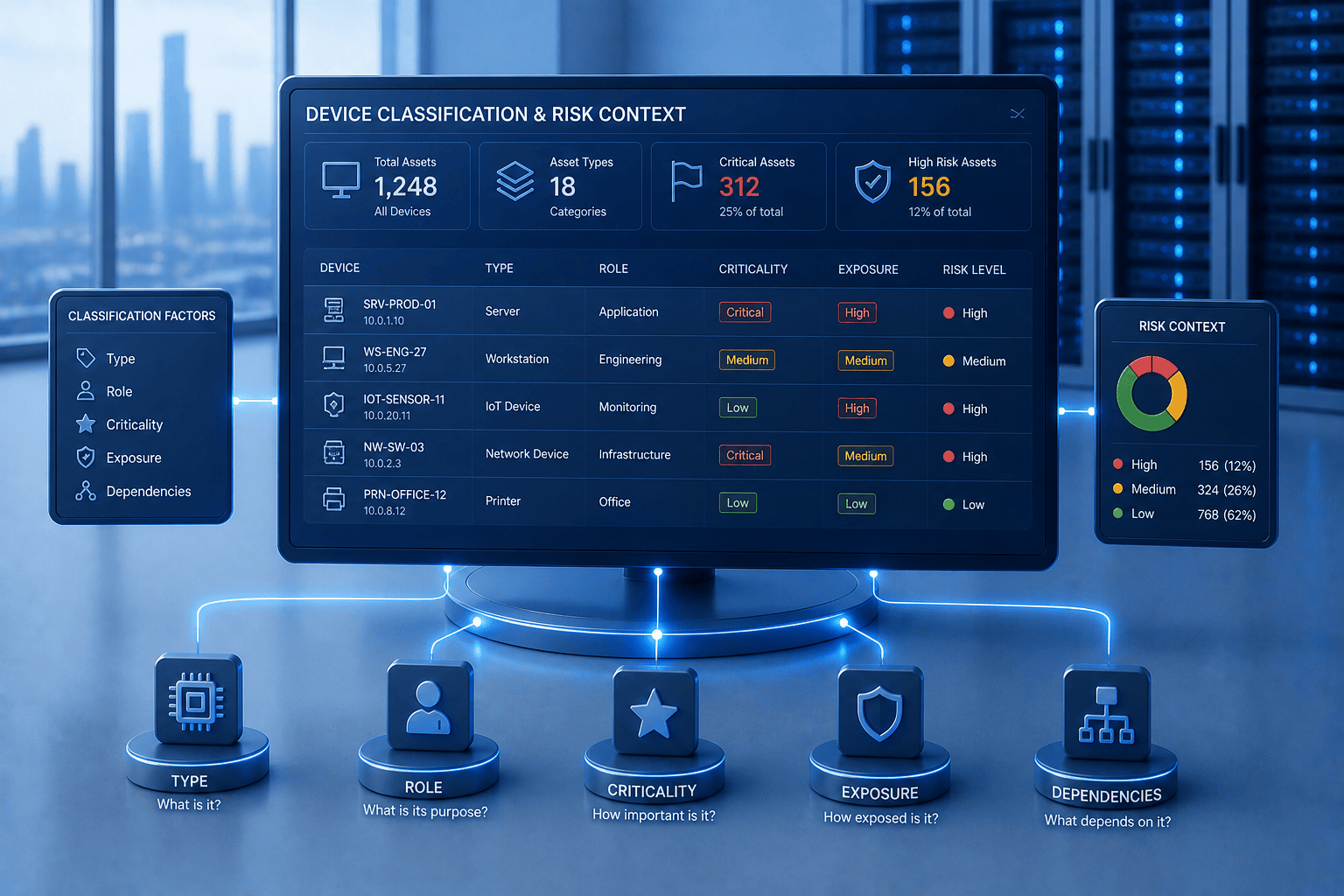
Device Classification and Risk Context
We classify assets by type, role, criticality, and exposure to provide meaningful operational and security context. This helps prioritize attention, understand dependencies, and identify devices that may require additional controls or remediation.
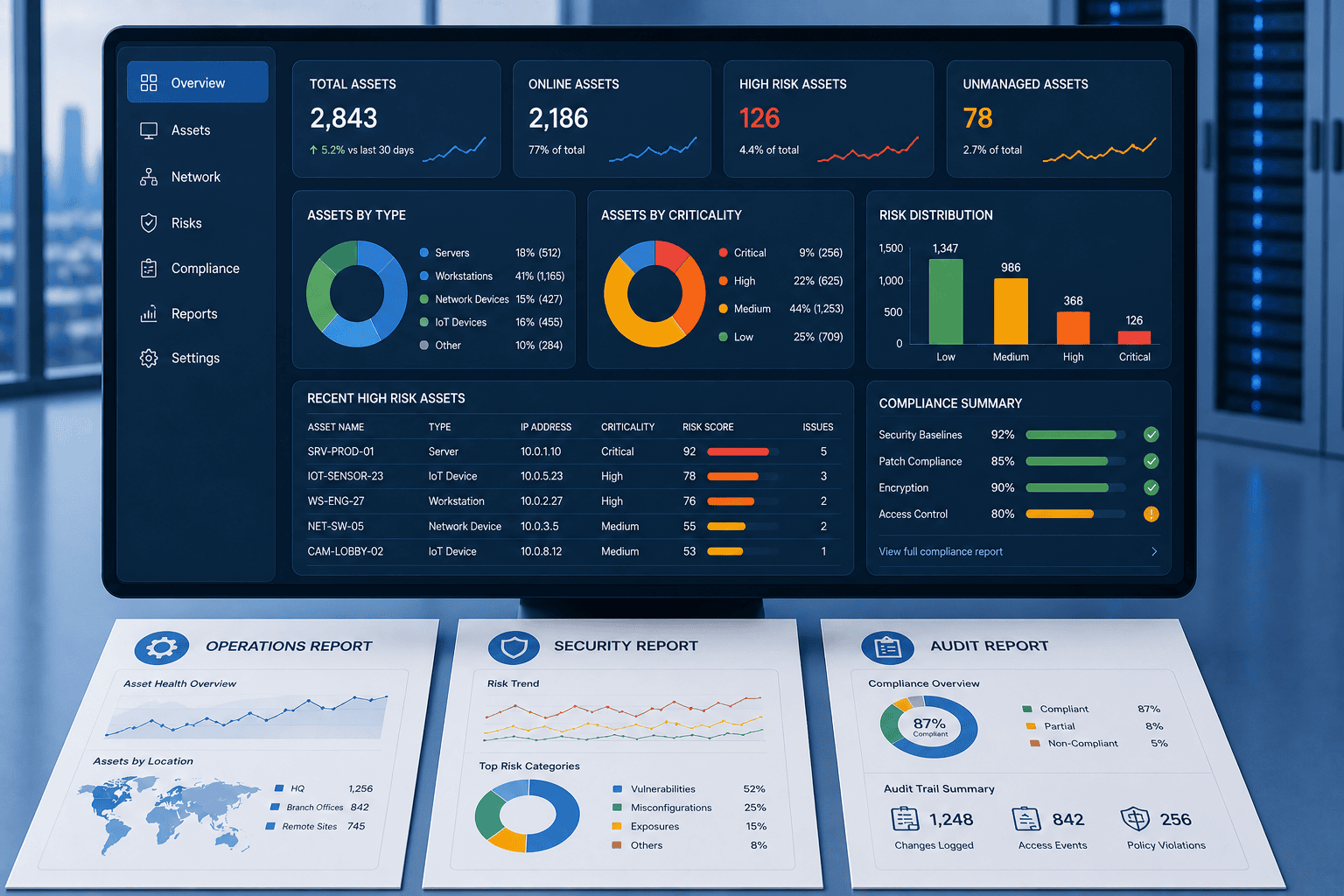
Reporting for Operations, Security, and Audits
We create structured reporting that supports IT operations, cybersecurity reviews, and audit requirements. Reports translate technical asset data into clear insights for infrastructure management, risk reduction, and compliance readiness.
How We Deliver
Our approach is structured, controlled, and aligned with real operational environments—ensuring that every solution is designed, deployed, and managed with full visibility and accountability.
Ready to Eliminate IT Blind Spots?
Gain clear visibility into your IT, network, and connected devices—so your teams can make better operational, security, and compliance decisions with confidence.





